The global pandemic profoundly affected our thinking and introduced new work paradigms. Now, remote working will continue for a very long time. In a way, it’s a profitable situation for both employers and employees.
With remote working, employees can have a better work-life balance because now they have more time to attend to their family chores and devote some time to their self-development.
Enhance data security during hybrid work
Learn moreRemote work saves huge costs in the form of office space, with ergonomic seating arrangements, transportation, electricity, and security expenses, all of which are saved by remote work.
Despite the numerous benefits of remote working, it still carries associated risk factors. One of the major risks with remote working is remote employee data security. Managing data protection while working from home can be a real business task.
Due to the quick rise of remote or hybrid working, cyber attackers can generate different kinds of viruses, which later cause data breaches.
For many businesses, transforming their working mode has been a tough decision mainly because of keeping their data secure.
One in three organizations has experienced a cybersecurity incident due to an unsecured remote employee. Approximately 90% of IT workers deem remote working unsafe, emphasizing the heightened risk for remote workers compared to on-site employees.
Table of contents
Security Issues With Remote Working
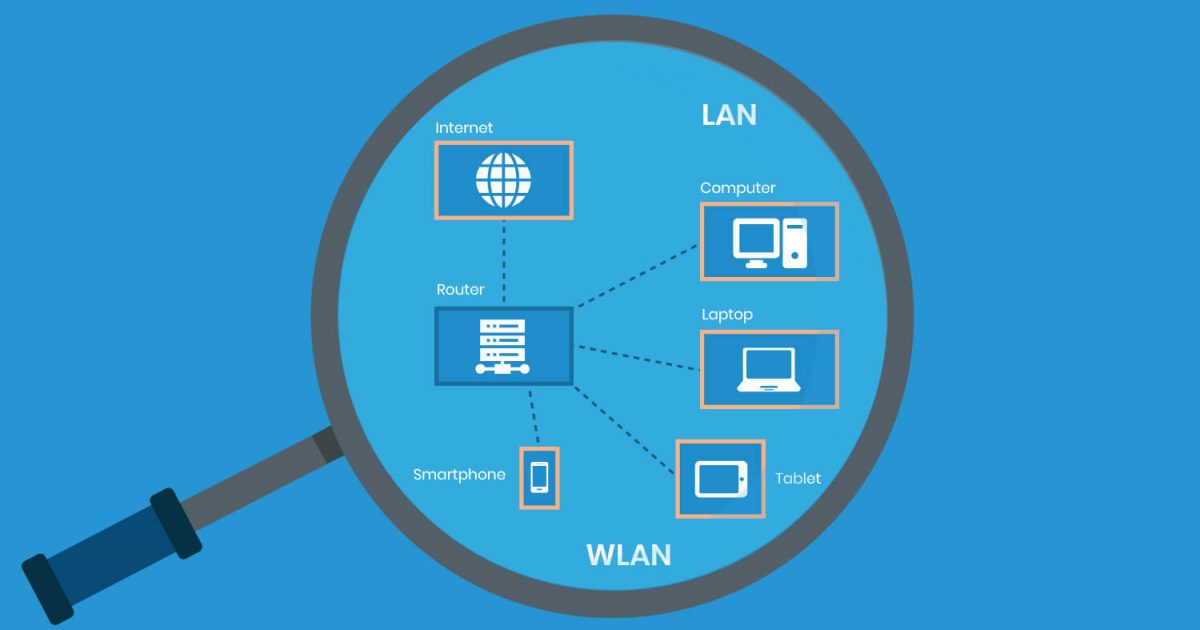
Regarding remote employee data security, companies are at a greater risk. Here are a few common security risks organizations face as they shift to remote work.
Phishing
It’s a common threat where hackers target employees by sending them messages and emails. Employees unwittingly install keylogging software on their PCs, allowing hackers to access business data.
Ransomware
Ransomware, a type of malicious software, encrypts files and denies access until individuals pay a ransom, coercing them to comply.
Advanced persistent threats
Hackers use this attack to invade the network by staying undetected for longer. This attack is effective because it makes it difficult to detect the hacker, enabling the theft of important data unnoticed.
Data Breach
It’s a security incident in which unauthorized members can access valuable data without authorization. A data breach can have severe consequences, compromising sensitive information and undermining organizational trust and security.
Solutions Provided By Artificial Intelligence in Data Security
As science and technology advance rapidly and the world goes digital, there’s a soaring demand for AI and ML.
With its increased demand, cyberattacks have also increased. The significant potential lies in AI-based biometric user authentication for logging into systems on mobile or computer.
Fingerprints, retina scans, and passwords are utilized for authentication, either with or without a password. Remote employees can undergo webcam scanning. AI can detect potential malware and ransomware, where AI is trained using complex algorithms to identify patterns towards potential cyber threats.
Just before any cyberattack occurs on the main system, it isolates itself to prevent damage. Companies have started using an employee activity monitoring tool, which helps them keep track of their remote employees and hire and train newly hired ones by ensuring data safety and security.
To prevent data breaches, such software consists of tools like website whitelisting, which allows the user only to use authorized websites, which halts every possibility of data leakage in a work-from-home setting.
Tools like key combinations allow administrators to block unnecessary key combinations to prevent data leaks among team members.
Cybersecurity experts consider remote employees threats because they are away from physical sight. Keeping track of remote employees and monitoring them for suspicious activity becomes challenging for organizations.
AI software assumes a pivotal role by incorporating features that enable organizations to monitor and track their remote employees and respond to any detected suspicious activity. These features not only help organizations increase the workplace productivity of their remote employees but also help restrict and take immediate action toward remote employees who seem suspicious.
If the system’s features detect any unusual behavior, it can capture users’ images from the webcam to identify impersonators. The system can employ screenshots and webcam images as evidence to identify unusual user behavior.
There are also features like remote barge-in, web usage & time tracking, which allow the person in charge or a supervisor to inquire into a user’s system to catch any malpractice or data leakages during their working hours. They will be able to monitor all online activities of active remote users and cease any possibility of data leakage in a remote working setup.
Conclusion
With the growing rate of cyber-attacks, organizations are becoming more aware and open to the importance of AI security tools like Leapmax.
Deploying artificial intelligence represents the intelligent and optimal strategy for safeguarding a company’s data, ensuring comprehensive protection in today’s rapidly evolving digital environment.